Please Wait
Loading..
Token Based Authentication
Manage your realtime data access with Token Based Authentication
-
When building real-time messaging apps, developers generally tend to consider client-side devices as untrusted.
-
Therefore, there are chances of credentials being compromised and developers need to work on minimizing the impact of the same.
-
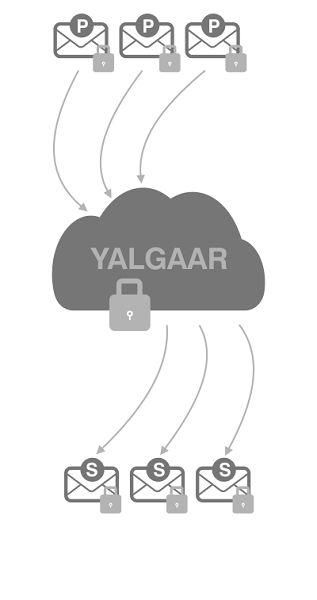
Yalgaar does helps developers achieve that objective by authenticating devices/users with the use of uuid tokens .
-
Such tokens only dispense the capability that is required for the device in question.
-
This makes it much simpler for developers to manage their real-time data access.
-
Most experts recommend token authentication because it delivers robust access control and strong security systems.
-
With Yalgaar, there are 3 types of tokens available. The first one is publish/subscribe prefix UUID.
-
This allows users to published message on channel and subscribe to channels. The second token is publish prefix UUID.
-
Under this, the users can only publish on a channel. Finally, the third one is subscribe prefix UUID.
-
As you might have guessed, this capability allows users to only subscribe to a channel.
The following functions make our messaging app worth your while
Manage Capabilities
As mentioned earlier, our tokens are issued with a particular capability in mind. This capability is on the basis of what the device in question needs.
Secure Access Control
Yalgaar’s token based system is secure. We are manging tokens at server side. Both these things help our developers in gaining better control over their app’s access.
Advanced Authentication
At Yalgaar, we don’t use the basic ‘Key-based’ method of authentication. We instead make use of token based access control in order to improve security and make your access control more reliable.
Why Would You Care?
-
Secure Mechanism - Developers now have a robust system of controlling who has access to different users.
-
Seamless Integration - Yalgaar’s token based access control system perfectly integrates with your existing authentication strategies. Therefore, you don’t need to work with a completely new system.
